How to limit login attempts on your WordPress site
If you have read any WordPress security hardening related article, you know that you need to somehow limit the number of login attempts a certain IP can make before it gets locked out, this is done to prevent malicious actors by gaining access to your site via brute force attacks. Due to WordPress’ popularity as a site building platform, attacks on it are pretty common. Luckily it’s pretty easy to protect your site from them and, of course, there’s a plugin for this!
WPS Limit Login
WPS Limit Login is a free and easy to set up plugin that prevents multiple login attempts by applying IP bans when a preset number of failed logins is reached.
After you install and activate the plugin you will find its options page under Settings > WPS Limit Login. You will be presented with the plugin’s configuration screen.
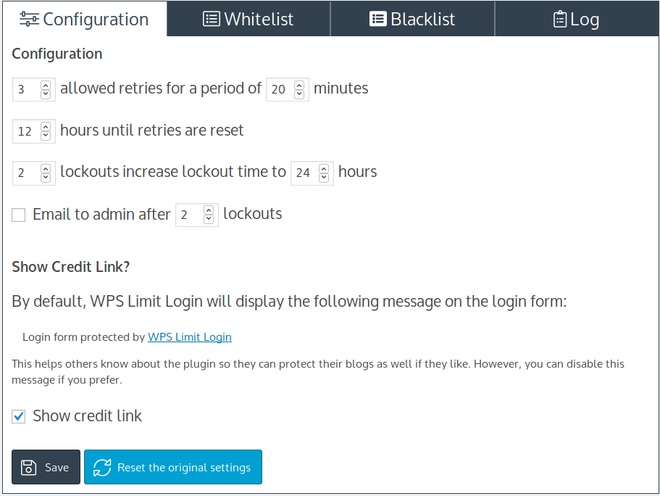
The set up consists from a handful of options. You can specify the maximum number of retries a specific IP can make in a given time period, the length of the first ban, the length of a subsequent ban if it occurs, and finally you can have the plugin send an email to the site’s admin if multiple bans are issued for the same IP, that’s about it, you can save and you are done. The plugin’s default settings are pretty sensible so if you don’t have any special needs for a particular site you can skip configuring the plugin altogether. The rest of the plugin’s tabs allow you to either Whitelist or Blacklist an IP (or IP range) should you so desire, and provide you will logs on lockouts issued by the plugin.
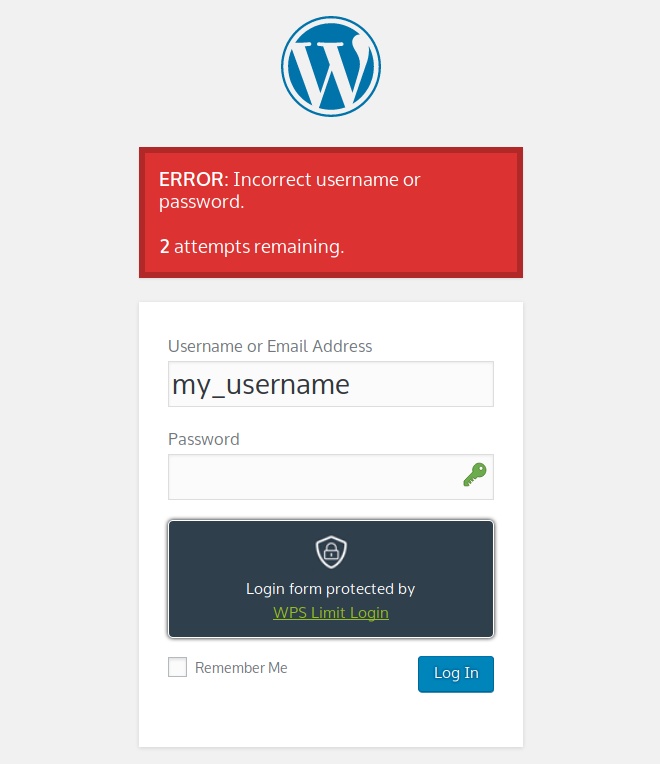
Now that the plugin is active and set up if you navigate to the login form you will see that it is being protected by the plugin. If a failed attempt is made, the user gets a notification informing them of the error and of the remaining attempts.
That’s it!
Your site is now protected against brute force attacks. Hopefully this guide will help you rid your site of unwanted login attempts and have one less thing to worry about. Have you got any ideas on topics you’d like to see discussed on our blog? Let us know in the comments below.
3 responses to “How to limit login attempts on your WordPress site”
Great Explanation. Everyone should read it. Please keep posting such a nice articles to help people.
Great short tutorial. I currently use UFW firewall combined with fail2ban on my ubuntu server to limit the login attempts too.
Saving checkbox “Email to admin after” does ot work for me.
Tried it several times , but the bx stays blank.
Removed plugin and use Limit Login Attempts Reloaded.